Technology Architecture
- The Aero-Factory Zones
- The Aero-Factory Security Strategy
- The Aero-Factory Deployment Models
- The Aero-Factory Infrastructure
- The Aero-Factory Metwork Topology
The Aero-Factory Zones
Logical isolation and multi-zone data brokering are the core of this single-instance architecture, designed to scale from a single terminal to a multi-airport enterprise hub.
1. The Flight Plant Zone (OT Zone)
- Air-Gapped Logic: Ensures the production of flights remains operational even if connectivity to higher IT layers is interrupted.
- Granular Segmentation: Supports internal isolation by airport terminal or infrastructure age, securely managing diverse hardware generations within a single instance.
2. The Flight Data Bridge (IDMZ Zone)
- Protocol Scrubber: Houses the Vortex Proxy components that isolate the OT production floor from the factory's IT layer.
- Secure Buffer: Acts as the primary gatekeeper, facilitating controlled data transit without direct zone-to-zone peering.
3. SkyUnity Local Zone (IT zone)
- Site-Specific Operations: Manages local business services like ticketing interfaces, carrier databases, and cargo systems for a specific physical location.
4. SkyUnity Corporate Zone (IT zone)
- Multi-Site Aggregation: Acts as the central authority, aggregating data from all SkyUnity Local Zones into a single, unified enterprise instance.
5. SkyUnity Cloud Zone (Cloud zone)
- Heavy Intelligence: Dedicated to ML/AI training and high-scale automation logic that extends the factory's analytical capabilities.
The Aero-Factory Security Strategy
Utilizing a Defense-in-Depth model, Aero-Factory ensures that both digital and physical assets are protected against evolving threats.
- Zero Trust Access (ZTA): No user or system, local or remote, is trusted by default. Identity-based access is mandatory for every data request within the Aero-Factory zones.
- Deep Packet Inspection (DPI): The Flight Data Bridge (IDMZ) inspects all traffic at the protocol level to identify and block malicious payloads before they reach the OT layer.
- Cyber-Physical Safety Interlocks: Hardware-level logic in the Flight Plant Zone that can override remote software commands to prevent physical accidents.
- End-to-End Encryption: All data is secured using AES-256 at rest and TLS 1.3 in transit, ensuring privacy from the runway sensors to the Cloud.
- Unified Identity Management: Centralized SSO and Multi-Factor Authentication (MFA) govern all administrative interactions across the entire Aero-Factory instance.
The Aero-Factory Deployment Models
Deployment Zones
The deployment model implements a hybrid, zoned architecture in which Perdue Levels 0–4 are permanently on-premises, Level 5 is deployable either on-premises or in the cloud, and Level 6 capabilities are cloud-native, enabling operational stability while supporting scalable digital innovation.
The deployment model is structured into three zones to separate workloads with fundamentally different operational, security, and scalability requirements.
The cloud-native enterprise and digital zone (Perdue Level 6) is dedicated to scalable, cloud-native capabilities such as analytics, data platforms, and digital services. Isolating these workloads in the cloud enables innovation and global optimization without introducing risk or dependency into industrial operations.
The enterprise hybrid zone (Perdue Level 5) provides a flexible layer for business and integration services that do not require real-time control. Allowing this zone to run either on-premises or in the cloud enables deployment decisions to be driven by business, regulatory, or cost considerations while maintaining a clear separation between OT systems and cloud services.
The on-premises industrial & site zone (Perdue Levels 0–4) hosts systems that interact with physical processes and therefore require deterministic performance, low latency, and high availability. Keeping these levels fully on-premises ensures operational continuity, safety, and independence from external connectivity.
These three deployment zones exist to ensure that operational stability, enterprise flexibility, and digital scalability can each be optimized independently, while preserving strong architectural and security boundaries between them.
Deployment Models
The deployment model is determined by key business constraints, specifically whether the Aero-Factory serves a single airport or multiple airports, and whether the terminals at each airport are interconnected via appropriate IT network.
-
Model 1: Single airport with embedded terminals
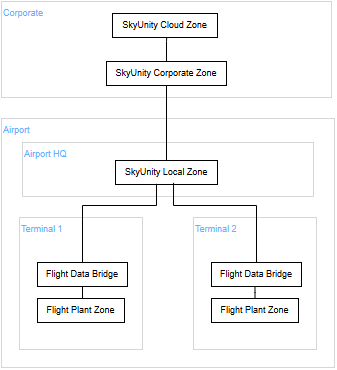
In this model, the airport operates as a unified architectural entity where all internal terminals are integrated under a single management umbrella. The Flight Plant Zones (Edges) and Flight Data Bridges (Proxies) at each terminal feed into a shared SkyUnity Local Zone (Site Hub) located on-premise, which serves as the consolidated gateway for the entire airport. This setup prioritizes operational efficiency and cost-optimization by centralizing the orchestration layer, allowing the SkyUnity Corporate Zone (Central Hub) to interface with the airport as a single, cohesive site. It is the ideal configuration for organizations seeking streamlined governance and simplified cross-terminal data aggregation.
-
Model 2: Single airport with isolated terminals
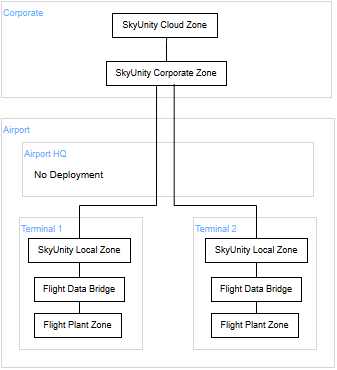
This model shifts the orchestration boundary downward, treating each terminal as a fully autonomous architectural unit. In this configuration (known as Multi-OT setup), the SkyUnity Local Zone (Site Hub) is deployed within the terminal's own infrastructure alongside the Flight Plant Zone (Edge) and Flight Data Bridge (Proxy), creating a self-contained three-zone stack on-premise. By decentralizing the Local Zone, the architecture eliminates inter-terminal dependencies and enhances fault isolation; however, it changes the corporate perspective, as the SkyUnity Corporate Zone (Central Hub) now recognizes and interfaces with each terminal as an independent site (e.g., "Airport 1, Terminal 1" vs. "Airport 1, Terminal 2"). This model is specifically engineered for high-security environments or large-scale hubs where terminal-level sovereignty and maximum operational resilience are paramount.
-
Model 3: Multiple airports (hybrid deployment)
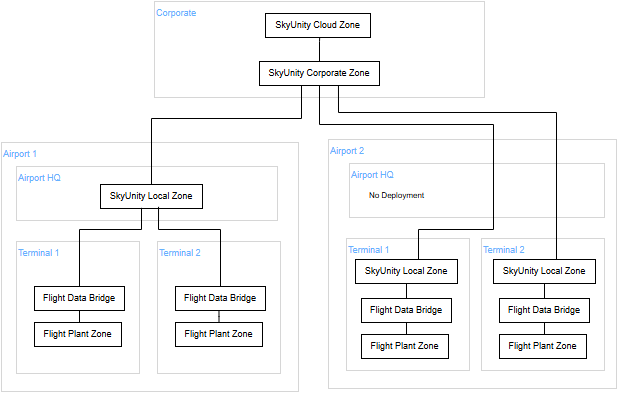
Aero-Factory may be deployed over multiple airports with embedded terminals, isolated terminals, or a mix of both (ilustrated on the diagram above).
This hybrid deployment model is designed for enterprise-level orchestration across a diverse portfolio of geographical sites, accounting for varying levels of local infrastructure maturity and regulatory requirements. In this setup, the SkyUnity Corporate Zone (Central Hub) acts as a global "Manager of Managers," seamlessly integrating multiple airports that may be utilizing either Model 1 (Embedded) or Model 2 (Isolated) architectures. This model supports connection to both shared Local Zones, serving multiple sites within a region, and dedicated Local Zones for high-autonomy terminals.
This tiered complexity is frequently mandated by National Operators and civil aviation authorities (such as ADP Group, Fraport, or Aena) that oversee vast networks of international hubs and smaller regional strips, requiring a unified "Cradle-to-Grave" trace while respecting the specific operational sovereignty of each individual site.
Key Observations: The "SkyUnity Local Zone" is the Pivot Point: In Model 1, it’s a shared service for the airport; in Model 2, it’s a dedicated service for the terminal.
Information Trace Continuity: In all three models, the "No Secrets" Principle remains intact because the data must pass through the Flight Data Bridge before reaching any version of the SkyUnity Local Zone.
Identity Management: In Model 2 and 3, unique Site IDs become critical as the SkyUnity Corporate Zone must distinguish between fragmented data sources from the same physical airport.
The Aero-Factory Infrastructure
The infrastructure is designed as a five-tier hierarchy that ensures total visibility and "Cradle-to-Grave" traceability of flight production data.
| Vortex Edge | Vortex Site Hub | Vortex Central Hub | Vortex Cloud Hub | Aero-Lakehouse | |
|---|---|---|---|---|---|
| Location | Immediately adjacent to the production line. | Local Data Center (on-premise) within the factory. | Regional/Corporate Data Center or Centralized Corporate Cloud. | Public Cloud Edge (Ingress Zone). | Centralized Corporate Cloud. |
| Hardware Type | Industrial Rugged PC (Fanless, IP67 rated if required). | Rack-mounted Server (Enterprise-grade). | Enterprise Cluster (Virtual or Physical). | Cloud Native Services (Gateway/Load Balancer). | Cloud PaaS (Managed Object Storage). |
| Compute Role | Lightweight Proxy, DPI Engine, Local Cache, Traffic Forwarding. | Application Gateway, Data Contextualization, Analytics, Alerting. | Global Orchestration: Routing, policy management, and site-to-site syncing. | Secure Ingress: Authentication, traffic scrubbing, and API management. | Big Data Analytics & Audit: Batch processing, ML, and final certificate generation. |
| Storage Strategy | NVMe SSD (Short-term buffer for resilience). | RAID/SAN (Hot/Warm operational storage). | Transient Message Queue: In-memory or high-speed cache. | Ephemeral Buffer: Short-lived staging area before commit. | Immutable Object Storage: WORM (Write Once, Read Many) policy. |
Tiered Technical Specifications
-
Tier 1: Vortex Edge (with Vortex Proxy)
-
Virtualization: Bare-metal Type-1 Hypervisor (KVM Lightweight) to isolate Vendor VMs.
-
Vortex Proxy (Integrated Component): A dedicated, hardened Vortex Proxy VM resides within this Tier. It acts as the local traffic mediator and protocol translator, intercepting vendor requests to ensure they adhere to the "No Secrets" security manifest before further transmission.
-
Deep Packet Inspection (DPI): Analyzes mirrored traffic to ensure protocols are documented, machine-readable, and unencrypted.
-
Traffic Slicing: Uses Open vSwitch (OVS) with port mirroring to "fork" vendor traffic, sending it simultaneously to its intended destination and upward to the Vortex Site Hub.
-
Resilience: If the connection to the Vortex Site Hub is interrupted, the local NVMe buffer caches the "information trace" to ensure no data gaps occur.
The Edge Node serves as the physical and logical "Choke-point" for all vendor communication.
-
Tier 2: Vortex Site Hub
-
Virtualization: Bare-metal Type-1 Hypervisor (KVM Enterprise/Cluster) to isolate Vendor VMs.
-
Data Synthesis: Aggregates vendor interactions into a unified Digital Thread for each flight. Contextualizes data before sending it to the upper Tier.
-
Security Enforcement: Detects unauthorized encryption or undocumented protocols "hidden" by vendors.
-
Data Persistence & Sovereignty: Acts as the "Local Fortress" for storage. Utilizing Enterprise-grade RAID/SAN systems, it maintains the hot/warm operational buffer of the "Cradle-to-Grave" trace, ensuring the factory remains legally compliant and audit-ready even during total cloud outages.
-
Cross-Proxy Aggregation: Orchestrates and synchronizes data streams from multiple Vortex Edge nodes (if exist) across production floors (terminals). It ensures that data from disparate vendor machines are aligned into a single, cohesive timeline for the entire site.
-
Site-Level Analytics: Hosts the local database and analytics engines required for real-time alerting and process monitoring. By processing contextualized data locally, it provides immediate feedback to plant managers without the latency of a cloud round-trip.
The Vortex Site Hub is the high-performance core that processes the raw data streams captured by the Edge.
-
Tier 3: Vortex Central Hub
-
Platform: Enterprise-grade Cluster (Virtual or Physical) situated in a Regional / Corporate Data Center or Regional / Corporate Cloud, designed for high-throughput routing and global policy enforcement.
-
Global Orchestration: Manages site-to-site synchronization and handles the distribution of security policies, ensuring that all Site Hubs operate under unified governance.
-
Traffic Management: Functions as a high-speed message broker and load balancer, optimizing the "handshake" between local Tier 2 infrastructures and the Tier 5 permanent archive.
-
Operational Bridge: Provides the logical link that allows the system to scale across multiple geographic locations while maintaining a single, centralized point for system observability and fleet-wide configuration.
The Vortex Central Hub acts as the enterprise-level traffic control center, orchestrating the flow of the Information Trace between multiple factory sites and the global cloud repository.
-
Tier 4: Vortex Cloud Hub
-
Platform: Cloud-Native Edge Services (Load Balancers & API Gateways) providing a robust and secure entry point for global factory telemetry.
-
Secure Ingress: Enforces strict authentication and authorization protocols, ensuring that only validated data from authorized Site Hubs can penetrate the enterprise network.
-
Traffic Scrubbing & Validation: Performs real-time inspection and sanitization of incoming data streams, protecting the internal "Permanent Fortress" from external cyber threats or corrupted payloads.
-
Ephemeral Buffering: Acts as a short-lived staging area that guarantees delivery to Tier 5 (Aero-Lakehouse), preventing data loss during peak load times or during complex database commit cycles.
The Vortex Cloud Hub serves as the secure gateway for all external data ingestion, providing the necessary infrastructure to scrub, authenticate, and buffer traffic before it enters the permanent archive.
-
Tier 5: Aero-Lakehouse
-
Platform: Cloud PaaS (Managed Infrastructure) providing infinite scalability and high availability.
-
Data Immutability: Utilizes WORM (Write Once, Read Many) storage policies to ensure that once a flight's information are synchronized, they cannot be altered or deleted by any vendor or internal actor.
-
Global Analytics & Audit: Hosts large-scale batch processing and Machine Learning (ML) models to perform cross-factory quality audits and predictive maintenance analysis.
-
Permanent Archive: Acts as the "Single Source of Truth" for the entire lifecycle of the product, moving data from the operational buffers of the Site Hubs into a permanent, regulatory-compliant vault.
The Aero-Lakehouse is the immutable destination of the Information Trace, providing a global repository for long-term governance and cross-site analytics.
Data Flow
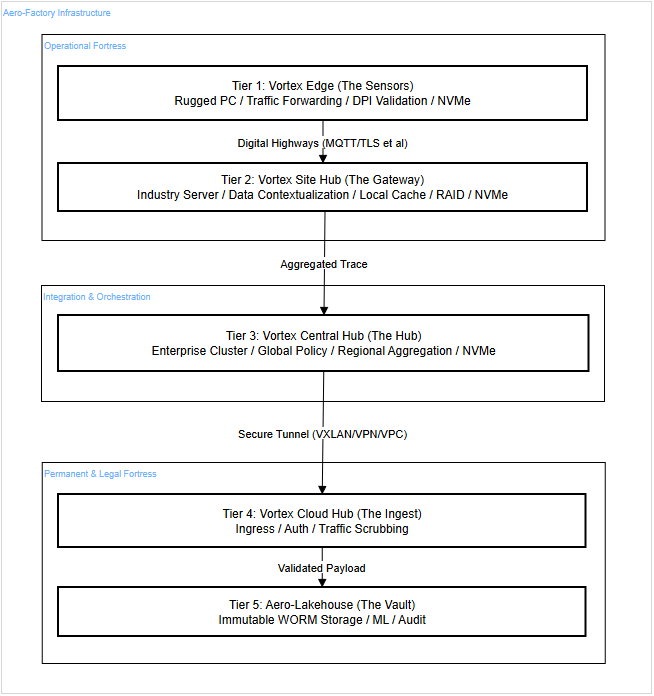
The Operational Fortress (Tier 1 & Tier 2)
The Operational Fortress represents the first line of defense and the primary point of value generation, located directly on the factory floor. This layer, comprising the Vortex Edge (with Vortex Proxy) and Vortex Site Hub, is designed as an autonomous entity that guarantees Local Sovereignty. Its core mission is to enforce the "No Secrets" principle through 100% data capture and real-time DPI (Deep Packet Inspection) validation. By utilizing industrial-grade hardware and NVMe buffering, this fortress ensures that no bit of information is lost due to network outages, while simultaneously shielding the integrity of the production process from external disruptions.
Integration & Orchestration (Tier 3)
The Integration & Orchestration layer acts as the intelligent "bridge" connecting physical production to the digital archive. Through the Vortex Central Hub, this segment of the architecture performs regional data aggregation and global Security Policy Enforcement. Rather than focusing on permanent storage, this layer prioritizes secure routing, traffic scrubbing, and fleet-wide configuration management. It is the dynamic engine of the system that enables scalability—transforming isolated factory "fortresses" into a unified, centralized ecosystem by optimizing the path of the Information Trace through encrypted tunnels toward its final destination.
The Permanent & Legal Fortress (Tier 4 & Tier 5)
The Permanent & Legal Fortress, embodied by the Vortex Cloud Hub and Aero-Lakehouse, serves as the terminal destination and the Immutable Source of Truth for the entire enterprise. At this level, data transitions from operational signals into permanent legal evidence through the strict application of WORM (Write Once, Read Many) policies. While it sits on high-performance cloud infrastructure backed by NVMe technology for rapid analytics, its true value lies in its unbreakability and long-term integrity. This is where the final "Cradle-to-Grave" product certification occurs and where advanced ML models operate, ensuring that the history of every manufactured unit remains protected against any retrospective alteration or tampering.
The Aero-Factory Network Topology
TODO
Next: Data Model